Android 11 introduced a protection for the installed apps list through a permission, treating it as sensitive personal data. In theory, any app wanting that information must request a special, tightly controlled permission. In practice, this post shows that a simple manifest trick allows apps to bypass those protections entirely and list almost all installed apps without asking the user, and without triggering Google Play’s review process. An analysis of the top 2,000 Google Play apps reveals that over 24.1% of apps already use this loophole. This post explains how the bypass works, how common it is, and why it is relevant for privacy and app security.

Why the list of your apps is so sensitive
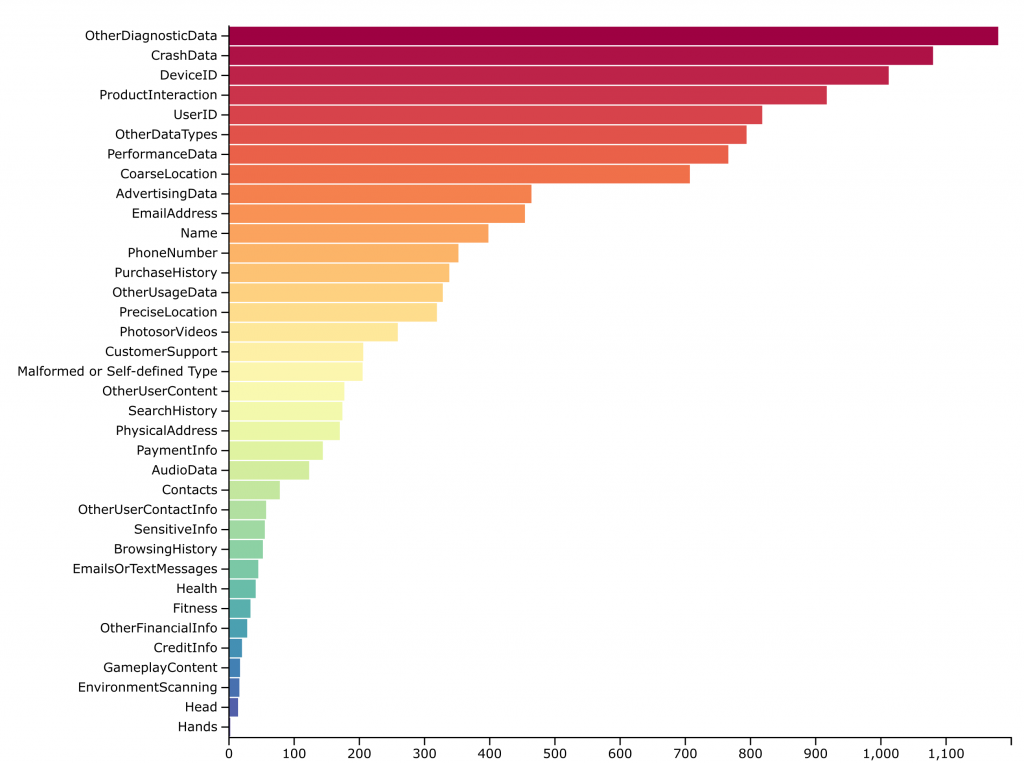
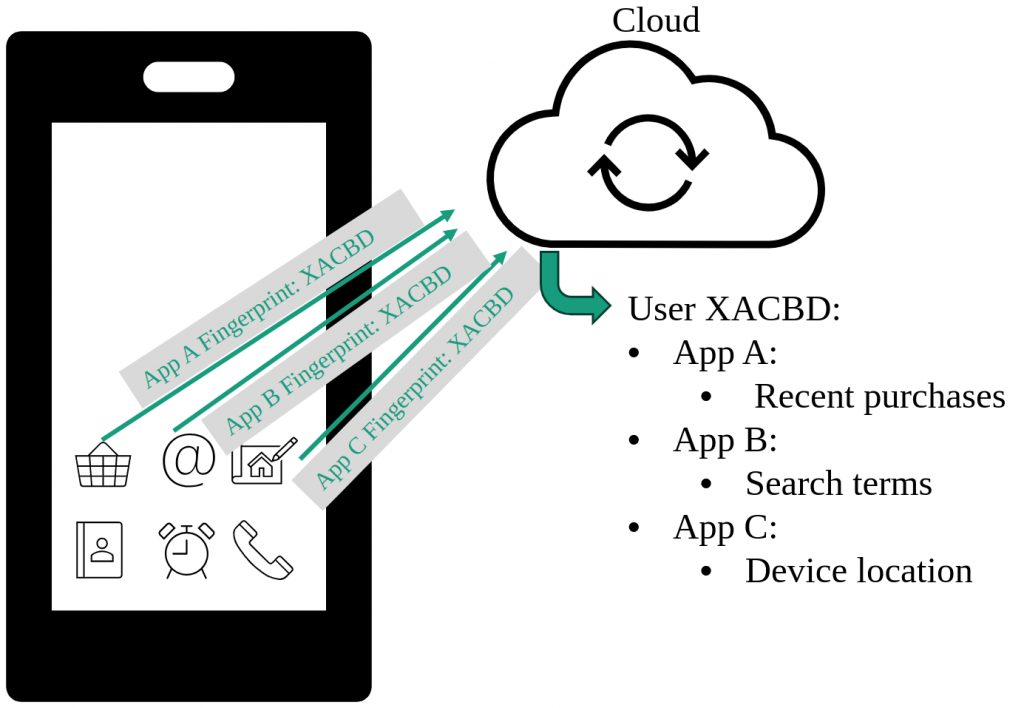
Smartphones store a huge amount of personal data, but it is not only your files and messages that are revealing. Knowing which apps are installed on your device already exposes a lot: your bank and insurance providers, health and fitness apps, dating apps, religious or political apps, shopping habits, and hobbies. Advertising and tracking companies have long used this “installed app list” as a form of personally identifiable information (PII). Especially the app list alone enables identifying: age (typical app target groups), gender (period tracker), ethnicity (bible app), living area (public transport app), personal interest (cooking recipes app), financial situation (banking/trading apps), commuting habits (petrol price tracker, airline app), used appliances (coffee machine, vacuum robot) and many more.
Google has responded to this by locking down access to PII such as IMEI, MAC address and stable device IDs. With Android 11, they added another piece: restricting access to the list of installed apps via the QUERY_ALL_PACKAGES permission. On paper, this looks like a strong privacy improvement. The work summarized here shows that, because of a design loophole, it is far less effective than it appears.
What Android tried to fix with package visibility
Before Android 11, any app could ask the system’s Package Manager for a full list of installed applications. That made personalized advertisement and profiling. With Android 11, Google introduced “package visibility filtering”. By default, an app can now see only a limited app set.
If apps really need to see all other installed apps, they should request the QUERY_ALL_PACKAGES permission. This permission is marked as high‑risk by Google. Apps that request it must justify the use and undergo manual review before being accepted on Google Play. The promise is clear: only a few justified apps should be able to see your full app list.
At the same time, Android still needs apps to communicate with each other. For example, a photo app must be able to find apps that can share or edit a picture. A file manager must find apps that can open PDFs. For this, developers declare “queries” in the app’s manifest that describe which types of other apps they want to see. This is usually based on intent actions such as “apps that can view PDFs”. This mechanism is meant to be narrow enough to support specific use cases without exposing everything.
The loophole: full app visibility without permission
The core finding is that the query system allows a manifest configuration that circumvents the protection for the installed apps list. By adding a specific intent query to the manifest, an app can list all apps that have a MAIN action. Almost every user‑facing app that appears in the launcher exposes this standard android.intent.action.MAIN action. Specifically, this query matches practically all apps a user has installed with just the following snippet in the manifest:
<queries>
<intent>
<action android:name="android.intent.action.MAIN" />
</intent>
</queries>
Thus, an app gains access to information about almost all installed apps, without requesting QUERY_ALL_PACKAGES permission at all.
We built a test app in two versions: one with the permission QUERY_ALL_PACKAGES, and one using this bypass query. On a real device, the version with the permission could see 696 apps, and the one with the bypass could see 606. The missing 90 apps were mainly low‑level system components without a launchable activity. Every user‑installed app that was visible with the permission was also visible via the bypass. Functionally, the supposedly protected data is still accessible without any permission.
How widespread is the installed apps permission bypass in real Android apps?
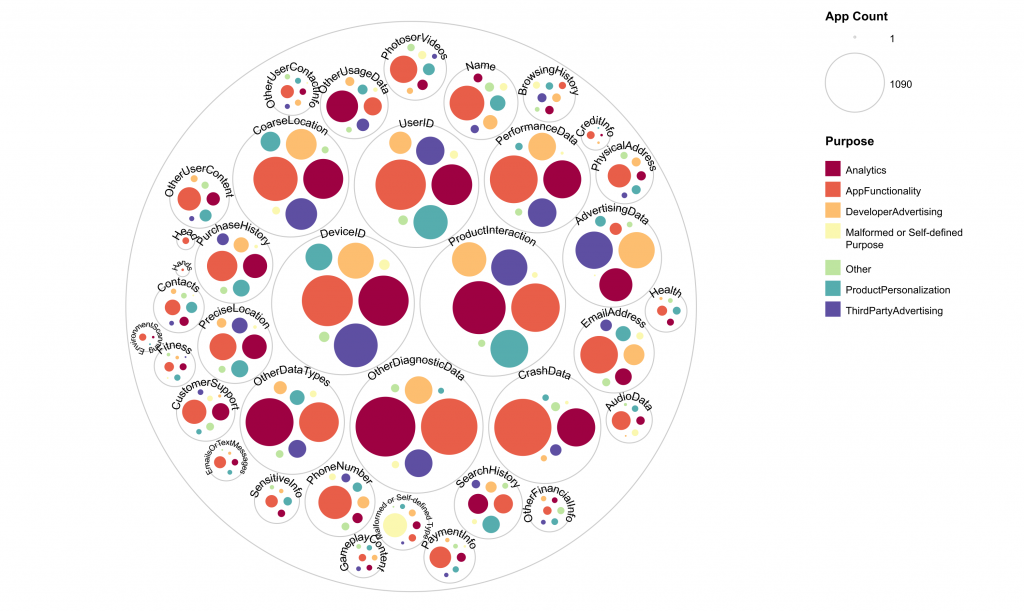
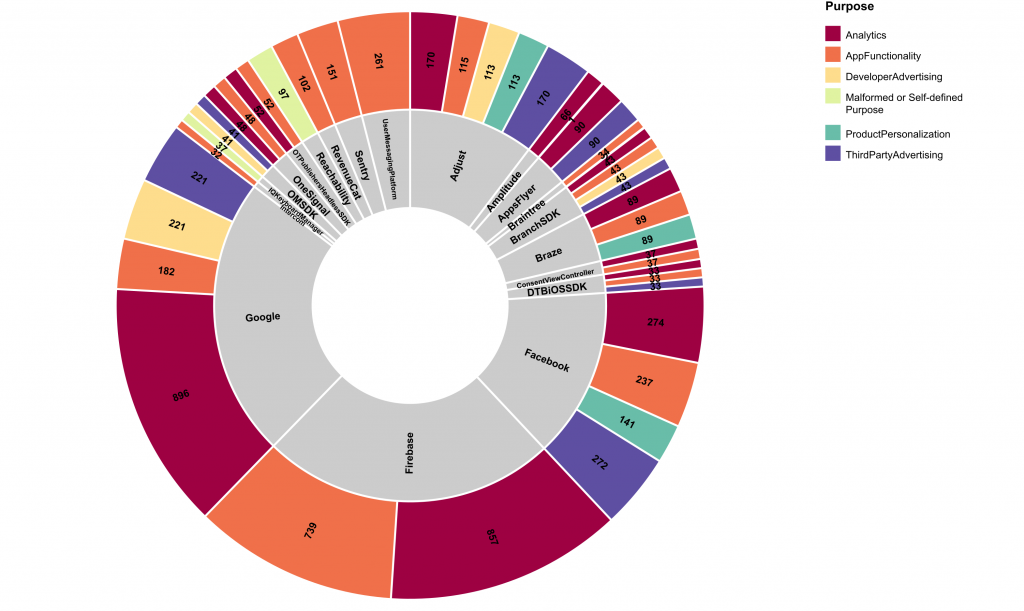
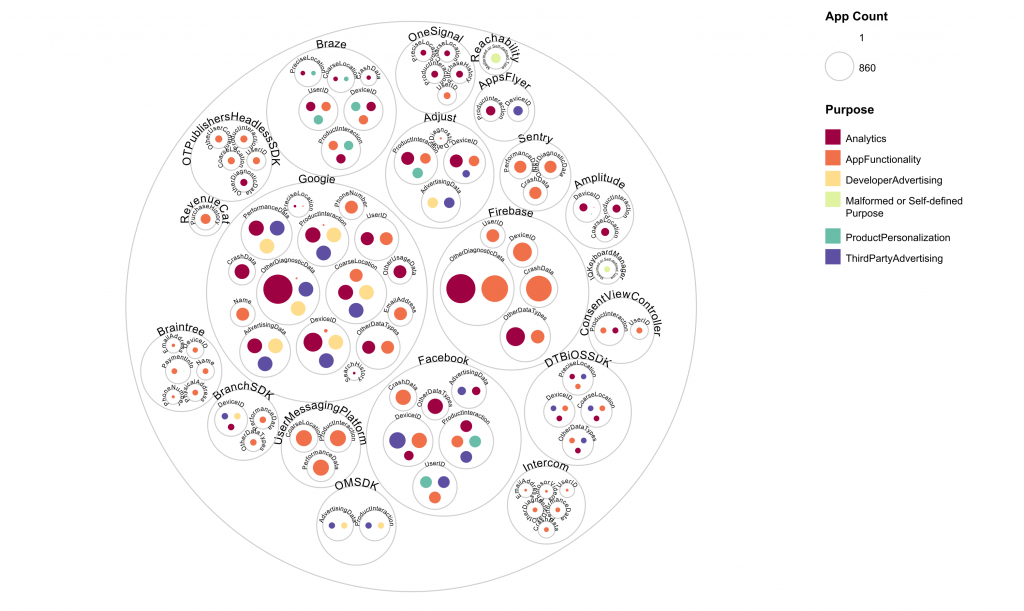
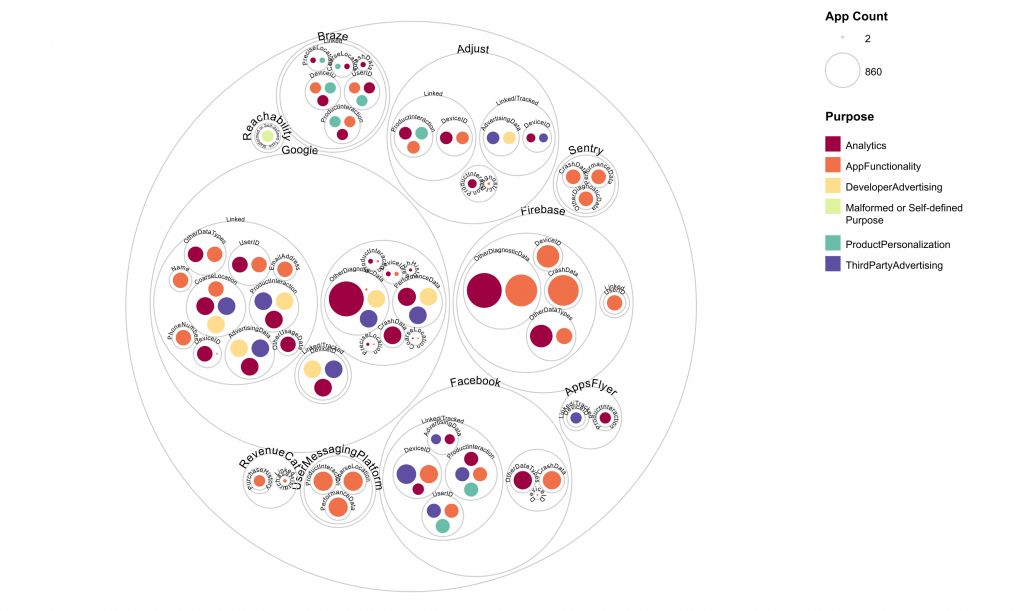
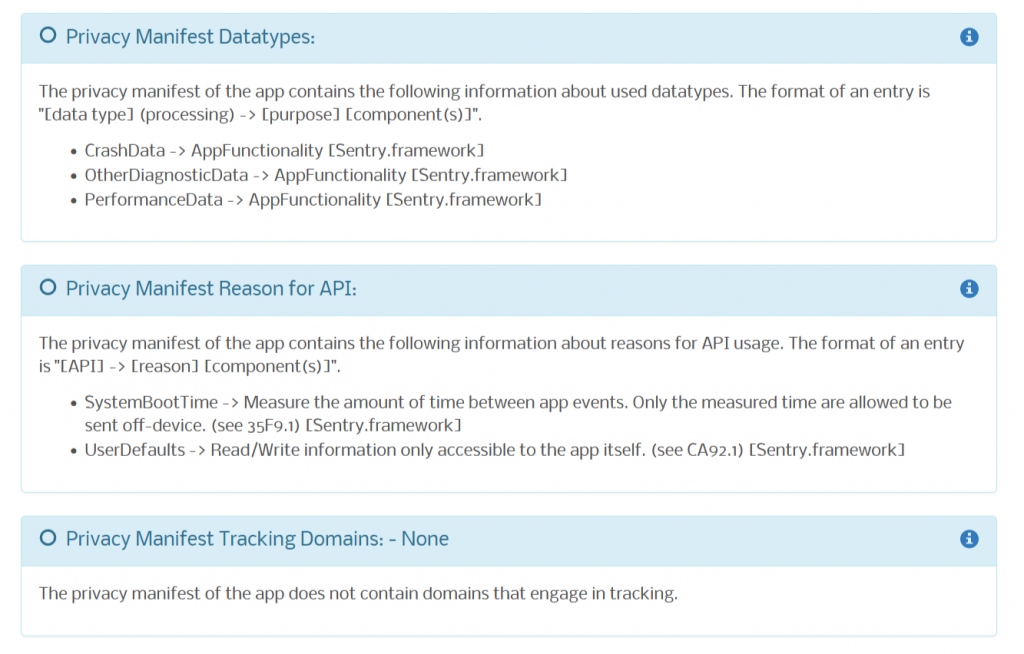
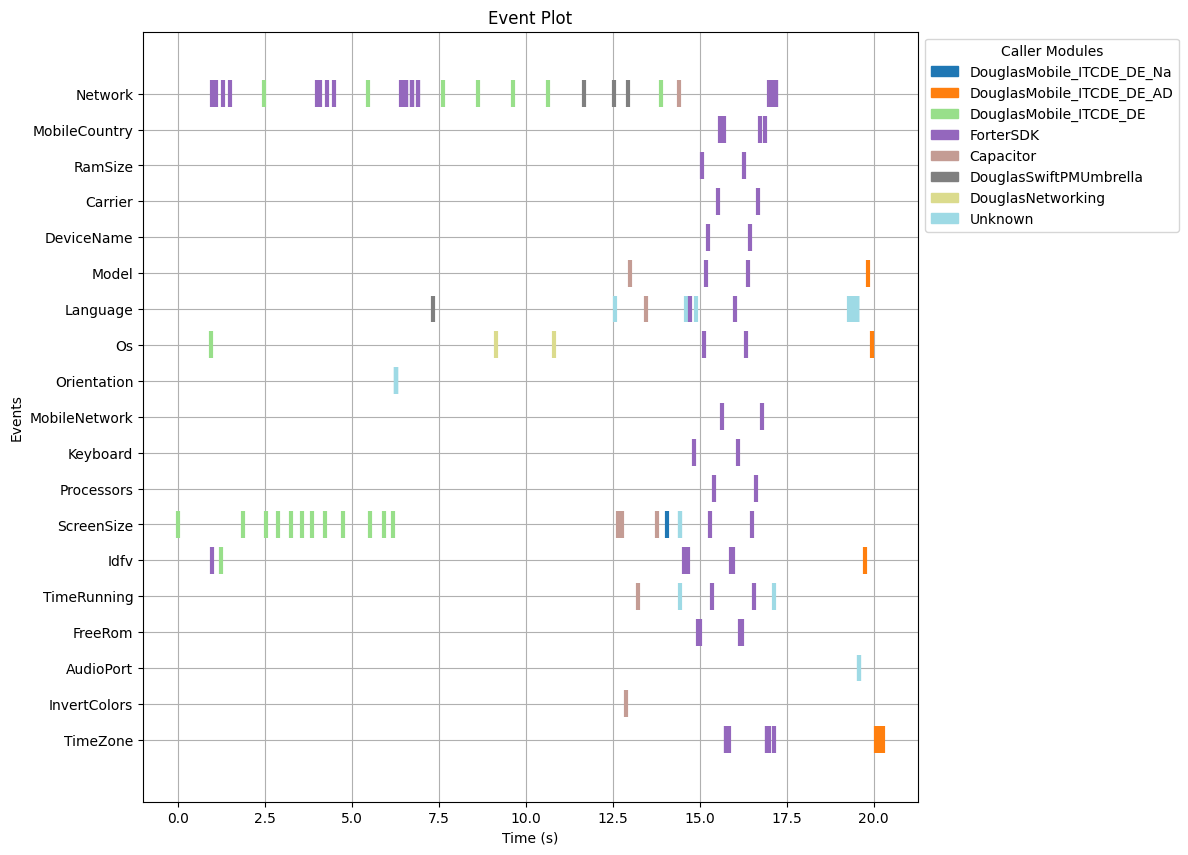
To understand how common this pattern is, we integrated an according analysis functionality into Appicaptor.
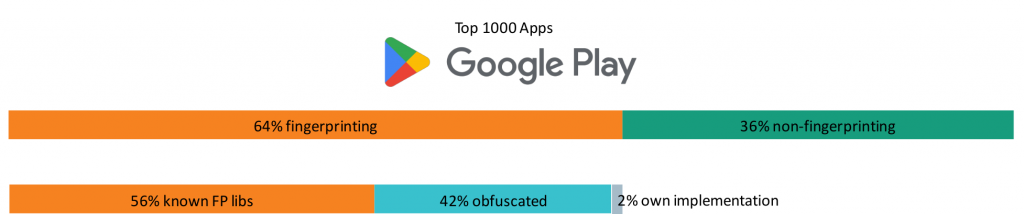
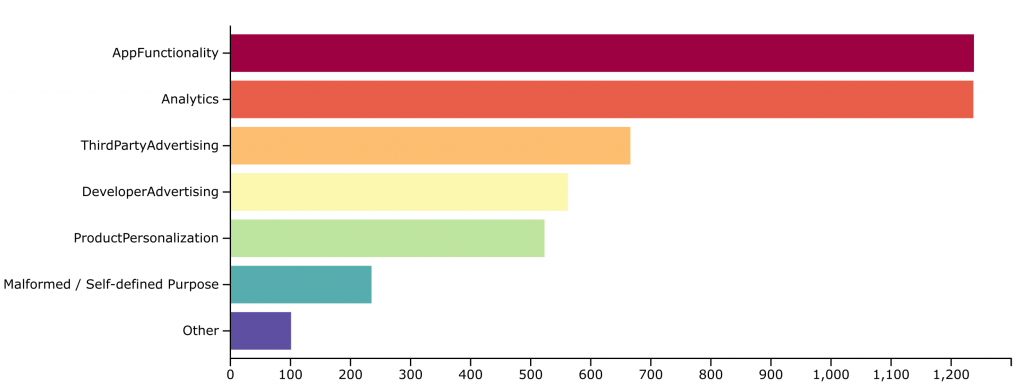
We applied this analysis to the top 2,000 Google Play apps with the following results. Only 0.7% of the tested apps don’t access the list of installed apps at all. More than 70% of the apps access a limited set of system apps preinstalled on the device. From a privacy perspective, this is still reasonable since these apps are no PII and apps often need to communicate with other system components. Almost 5% of the tested apps go through Google’s tedious approval process to cleanly access the list of installed apps through the QUERY_ALL_PACKAGES permission.
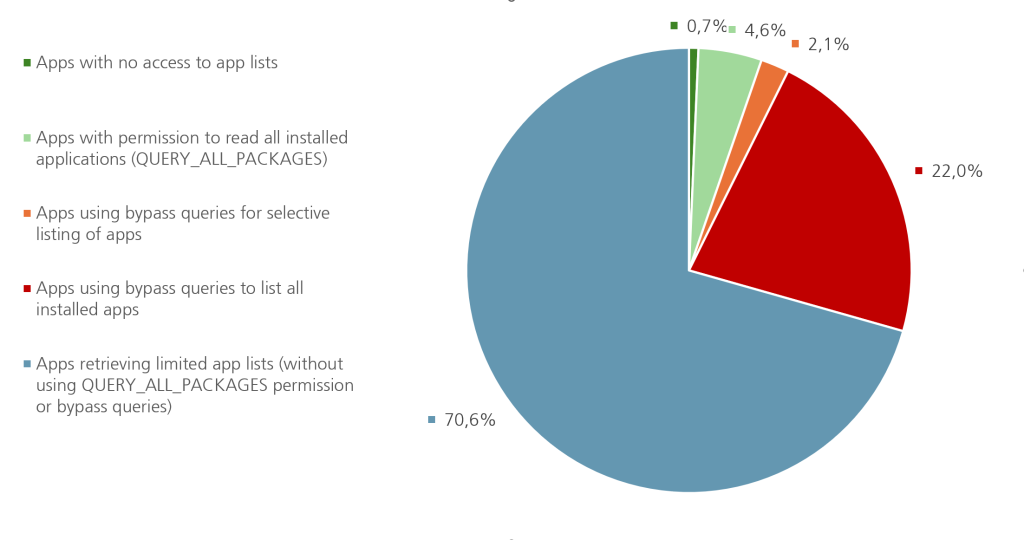
The results on the bypass to app list are striking. While only 4.6% of the apps requested the official permission, 24.1% of the apps use the bypass. So apps are roughly six times more likely to use the loophole than to go through the regulated permission pathway.
Among the apps using the bypass, 91% explicitly called Package Manager functions that retrieve full lists of installed apps. Only 9% used selective queries that narrow down the returned list to specific apps of interest, which is more privacy preserving.
Google’s response and the policy contradiction
We reported the bypass to Google via the BugHunters program as a potential privacy vulnerability. Google’s response was that querying packages via an intent action is “working as intended” and is not considered a security issue. At the same time, Google’s own documentation treats the installed app list as “personal and sensitive user data” and requires strong justification and review for the QUERY_ALL_PACKAGES permission.
This leads to an odd contradiction: Google enforces strict controls on one way of accessing installed app lists, while leaving essentially equivalent access open via another mechanism. It even uses the broad intent query pattern in official example code for their advertising SDK. Developers copying these examples may unintentionally give their apps and libraries much more visibility into user devices than needed.
What should change, and what you can do now
To make Android’s package visibility protection meaningful, the platform needs to align the enforcement with its privacy goals. Either broad queries like the generic MAIN intent should be disallowed or restricted, or using them should be treated like requesting QUERY_ALL_PACKAGES, with the same review and policy checks. Otherwise, the permission system and Google Play disclosures cannot be trusted as indicators of what an app can really learn about a device.
Until that happens, individual users have little direct visibility into this behavior. Organizations, however, can use Appicaptor which detects this bypass, and put apps using this technique on their block list for managed devices.
Conclusion
In summary, Android’s protection for the installed app list is currently more of a speed bump than a barrier. A simple manifest configuration gives many apps near‑complete visibility into what you have installed, without your knowledge and without Google’s stricter controls kicking in. As long as this loophole remains open, platform privacy promises around app visibility should be treated with caution and carefully verified, rather than assumed.
Further insights on our used detection mechanism can be read in our extensive paper “Permission Granted? How Android’s App List Protection Fails in Practice” at Springer (to be published in May), presented at the ESORICS conference Workshop MIST 2025.