As mobile app usage grows, so do concerns about security vulnerabilities. One significant aspect contributing to these vulnerabilities is the inclusion of third-party libraries in app development. In this article, we explore the importance of monitoring vulnerable third-Party Libraries in apps, and conducting risk analysis based on that information. Appicaptor analyses unveil that numerous apps include third-party libraries in versions known to have vulnerabilities. What’s more troubling is that some of these vulnerable versions are known to be attackable for years.
Third-party libraries are pre-existing code modules or components developed by external parties. Developers integrate these libraries into their applications to streamline development, enhance functionality, or access specialized features. Ranging from simple utility functions to complex frameworks, third-party libraries serve as building blocks for mobile app development. While beneficial, they also introduce dependencies that can impact the security of the app.
Like any software component, third-party libraries can contain vulnerabilities that malicious actors exploit to compromise the security of the app and its users. These vulnerabilities may arise due to coding errors, insecure configurations, outdated dependencies, or inadequate security practices during development.
Finding Vulnerable Third-Party Libraries
Appicaptor executes an evaluation of iOS and Android apps including their third-party libraries and their impact on app security by:
- Recognizing included libraries and their versions: Identifying the included third-party libraries and their specific version in Appicaptor. This identification is based on the analysis on the iOS or Android app’s binary, the library signatures, class/method structures and metadata.
- Library Vulnerability Lookups: With the third-party libraries and versions identified, Appicaptor holds a database with information about known vulnerabilities found within third-party libraries broadly utilized in the iOS or Android app development landscape. By referencing sources such as CVE entries, Appicaptor compiles the list of known vulnerabilities and weaknesses relevant to the app’s third-party dependencies.
Vulnerable Third-Party Library Analysis
In the following we present the Appicaptor results analyzing the 2,000 most popular free apps for iOS evaluating app libraries and JavaScript libraries.
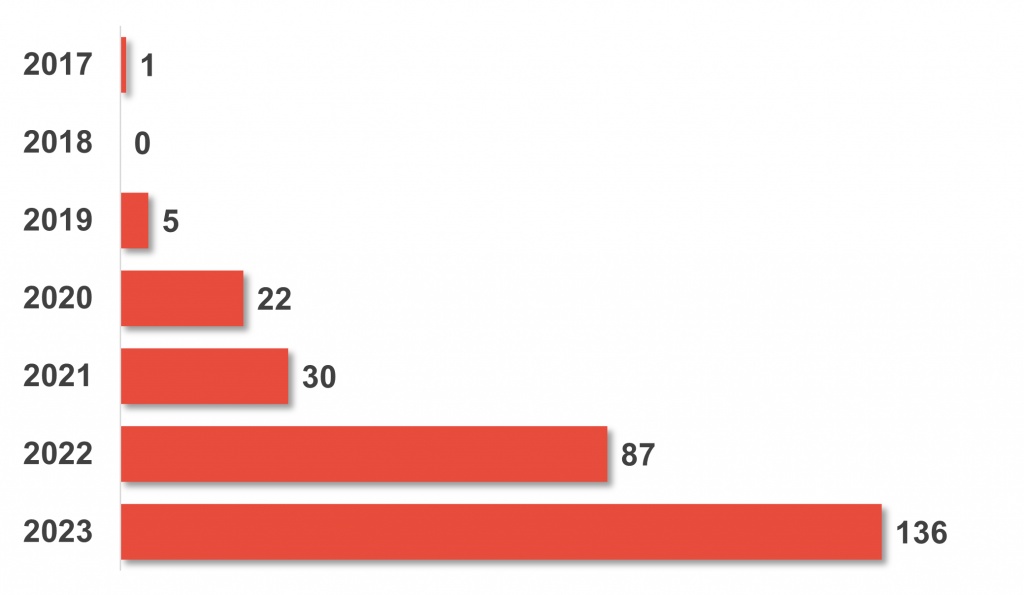
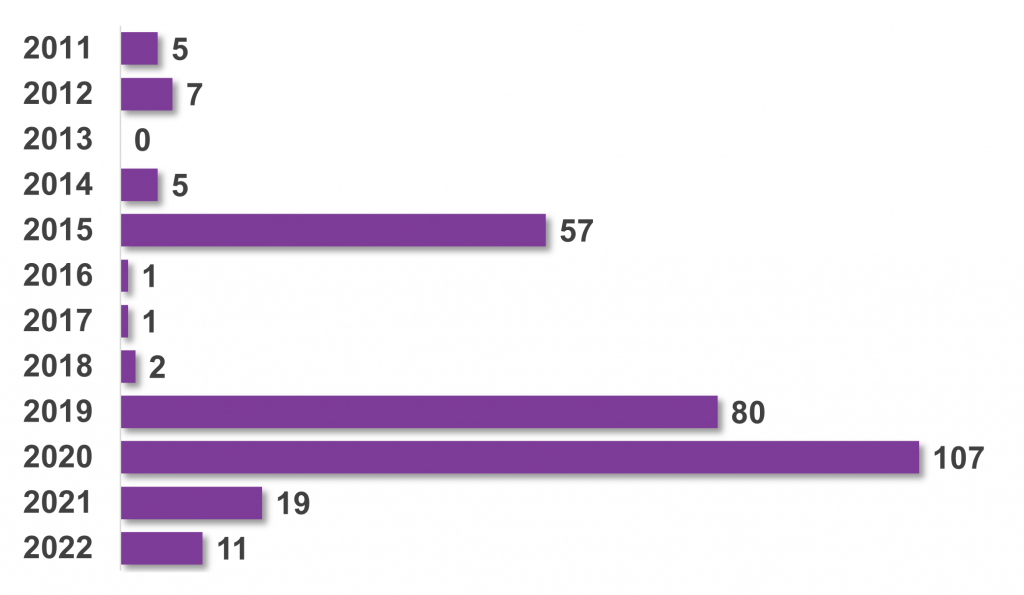
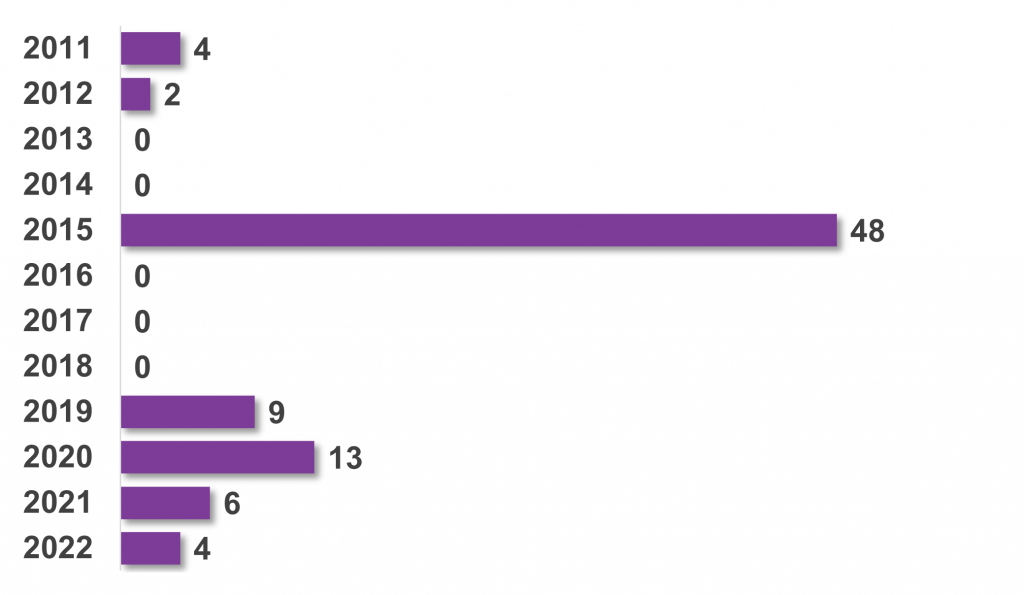
The initial aspect under evaluation pertains to determining the extent to which discovered vulnerable library versions have been recently published or have been known for an extended period. This inquiry aims to gauge the likelihood of vulnerability resolution, with a high number of recent CVEs suggesting a higher probability of fixes compared to older CVEs. Our methodology involved finding all vulnerable library versions across all analyzed apps and examining the publication year of each CVE of these vulnerable library versions. Then we aggregated the occurrences of applicable CVEs for each year, which were then plotted on a graph.
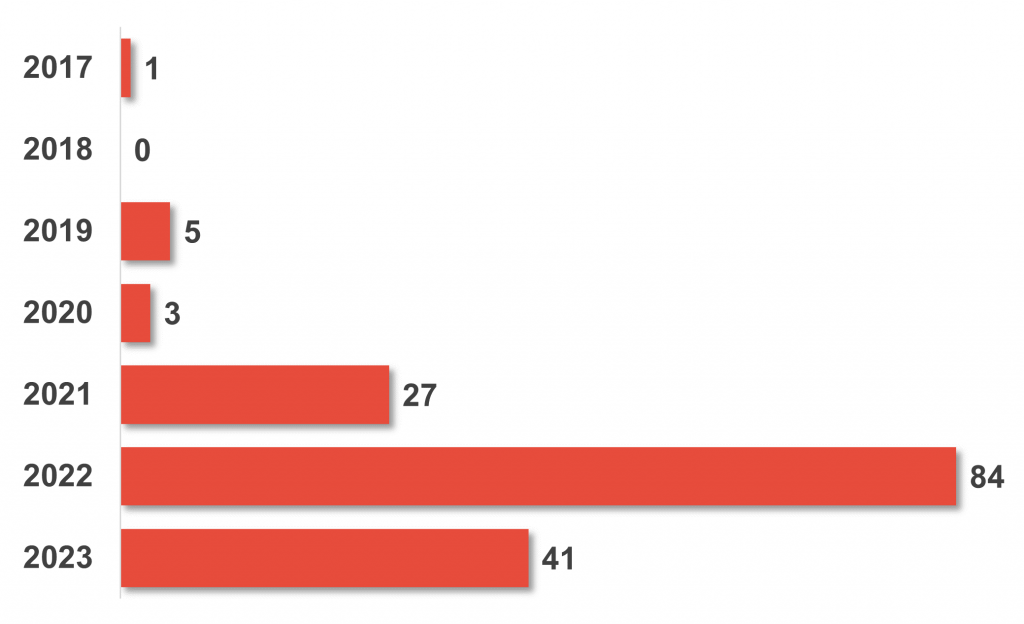
The second graph focuses on another facet: the age of the oldest CVE found in each app containing vulnerable library versions. This aspect addresses the duration during which an app might remain susceptible to attacks. To accomplish this, we identified the oldest CVE entry for each app featuring vulnerable third-party library versions, and subsequently plotted the sum of occurrences/apps for each year.
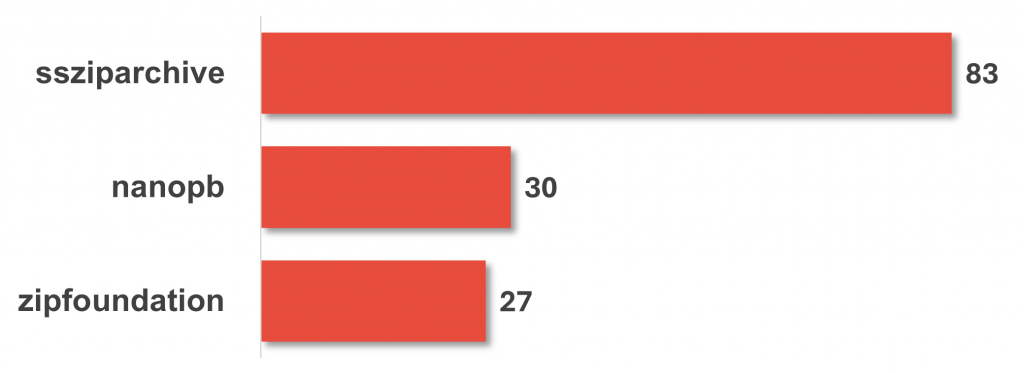
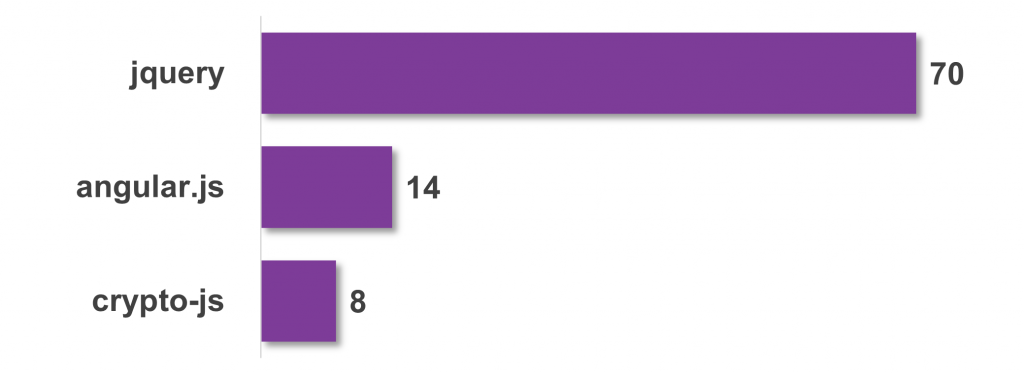
Lastly, the final graph delves into identifying the libraries primarily responsible for vulnerabilities in apps, as they are integrated more frequently in versions containing vulnerabilities.
App Libraries Results
Among the 2,000 most popular free iOS apps analyzed, 161 were discovered to have one or more vulnerable versions of app libraries. Assessing the timeline of vulnerability disclosures for each identified vulnerable third-party version within these top-tier iOS apps reveals two key trends: Firstly, certain apps feature multiple vulnerable third-party app libraries, indicating potential widespread susceptibility. Secondly, there appears to be an ongoing effort to patch these vulnerabilities, as evidenced by the increasing total number of CVE-listed vulnerabilities for the 2,000 evaluated apps versions from past to present. This suggests that patched versions of the libraries are being adopted in app updates as they become available, thereby mitigating security risks over time. But we also found occurrences of old CVEs (including our 2019 published TwitterKit vulnerability). The vulnerable versions of app libraries predominantly used in the 2,000 most popular free iOS apps mainly issue communication and data management, with notable examples being nanopd, ssziparchive, and zipfoundation.
JavaScript Libraries Results
In contrast to the app library evaluation, the analysis of vulnerable JavaScript library versions within the top 2,000 free iOS apps reveals a different scenario. Only 81 apps include vulnerable JavaScript library versions, but these vulnerabilities tend to persist for longer periods. We found 74 occurrences of CVEs that were published nine or more years ago. The chart presenting the oldest CVE for each app shows a similar result: 54 apps include at least one vulnerable JavaScript library version whose vulnerability was published nine or more years ago. The most found vulnerable JavaScript library versions primarily revolve around two key libraries: jquery and angular.js.
Conclusion
Monitoring and evaluating third-party libraries are critical components of mobile app security. The presented results show on the one hand, that certain libraries are included in a reasonable number of apps with vulnerable versions. This adoption of vulnerable library versions in popular apps raises serious concerns regarding the security posture of the applications and the data they handle. On the other hand, vulnerable library versions remain far too long in apps after the vulnerability has been published. Even as developers strive to introduce new features and improve user experience, security vulnerabilities often linger, posing a persistent threat to user’s data and privacy.
